MetaCTF - Not So Private Browsing 2
A follow-up CyberCorp challenge combined Morse code audio, Base64 encoding, and a Vigenère cipher. Decoding each layer in sequence with CyberChef and an online Morse decoder recovered the flag.
Challenge
Platform: MetaCTF Category: Crypto Points: 150
CyberCorp had upgraded their encryption after the first memo was cracked. The IT Department sent a new memo to their CISO containing a Base64-encoded ciphertext. A separate morsecode.wav file was provided as a voicemail reference - the memo instructed the recipient to apply the key left in their voicemail to decode the message.
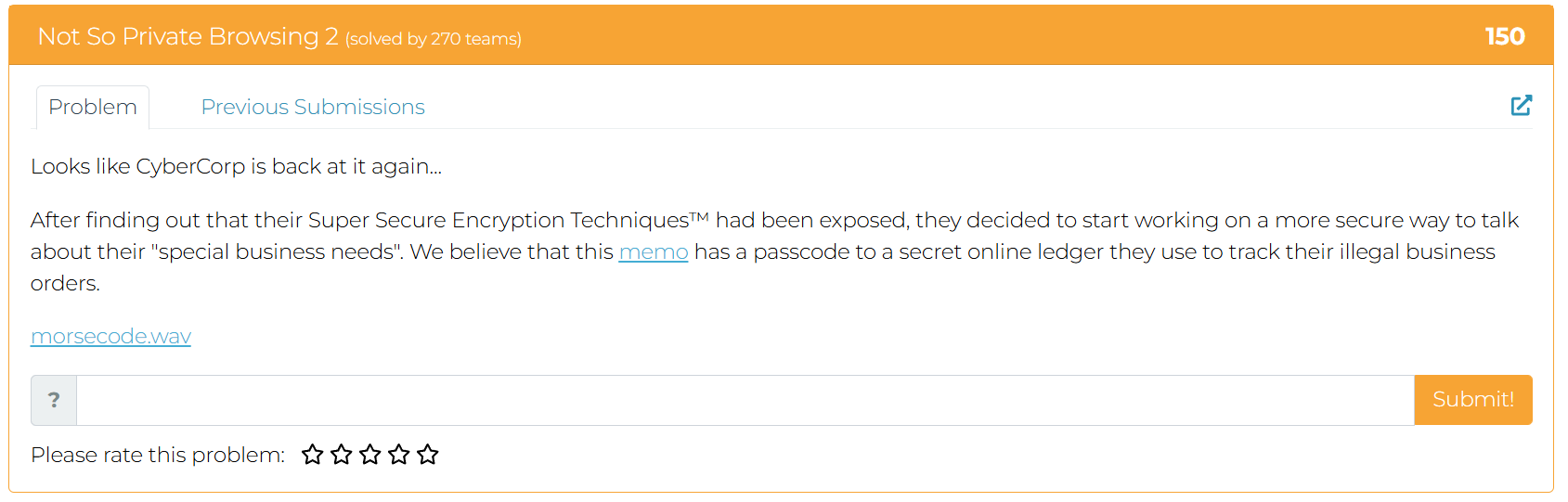
Challenge card – 150 points, solved by 270 teams
The Memo
The memo was addressed to Carl Ince (CISO) from the IT Department, dated February 5th, 2021. The subject was “Code Repository Access.” It referenced cipher specialists in France and instructed the recipient to apply the key from their voicemail to the encoded message for access to a new internal code repository.
The ciphertext in the memo:
UGl5Y1FHVHt2cXN2dHhzcV9tcnhfXN5X2thY3NhaXd2ZmR6cn0=
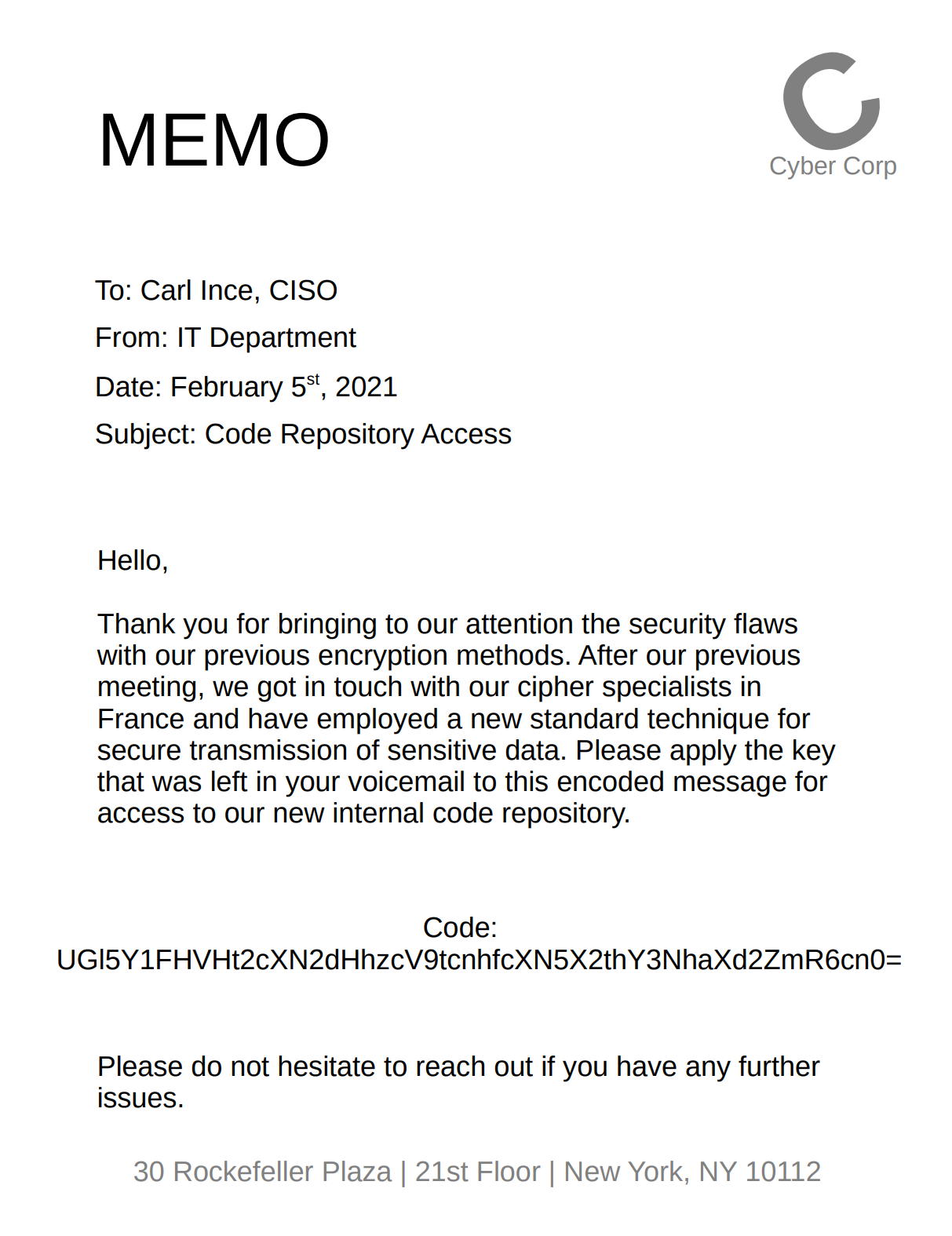
The leaked memo – ciphertext to be decoded with a key from a voicemail
Finding the Key
The challenge included a morsecode.wav audio file described as the voicemail containing the decryption key. Uploading it to an International Morse code audio decoder tool revealed the message:
DEFCONONE
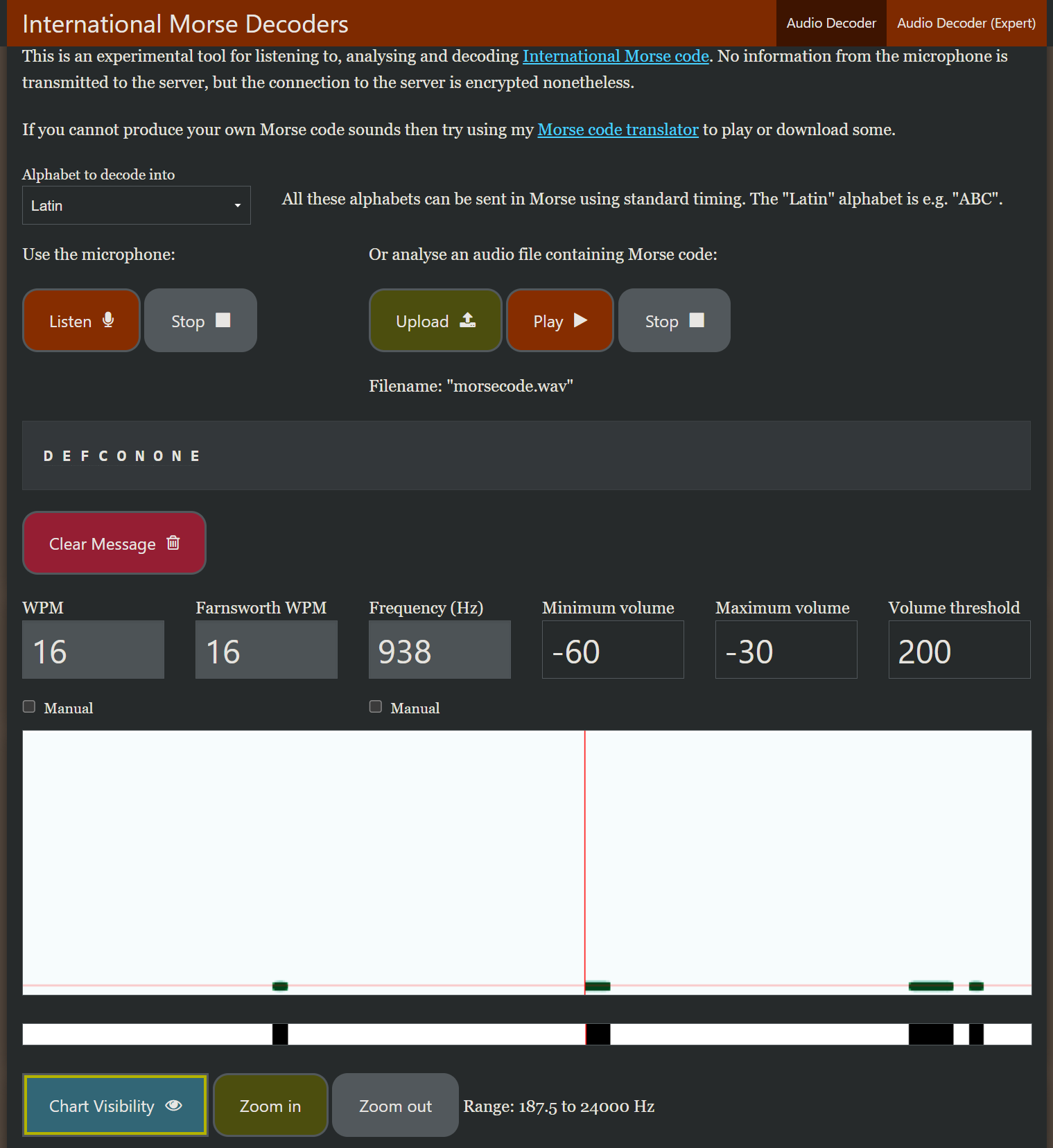
Morse audio decoder – voicemail key decoded as DEFCONONE
The reference to “cipher specialists in France” in the memo was a hint toward the Vigenère cipher, which was invented by Blaise de Vigenère, a French diplomat and cryptographer.
Decoding
Step 1 - Base64
The trailing = padding on the ciphertext is a strong indicator of Base64 encoding. Decoding it in CyberChef revealed the intermediate ciphertext:
PiycQGT{vqsvtxsq_mrx_qsy_kacsaiwvfdzr}
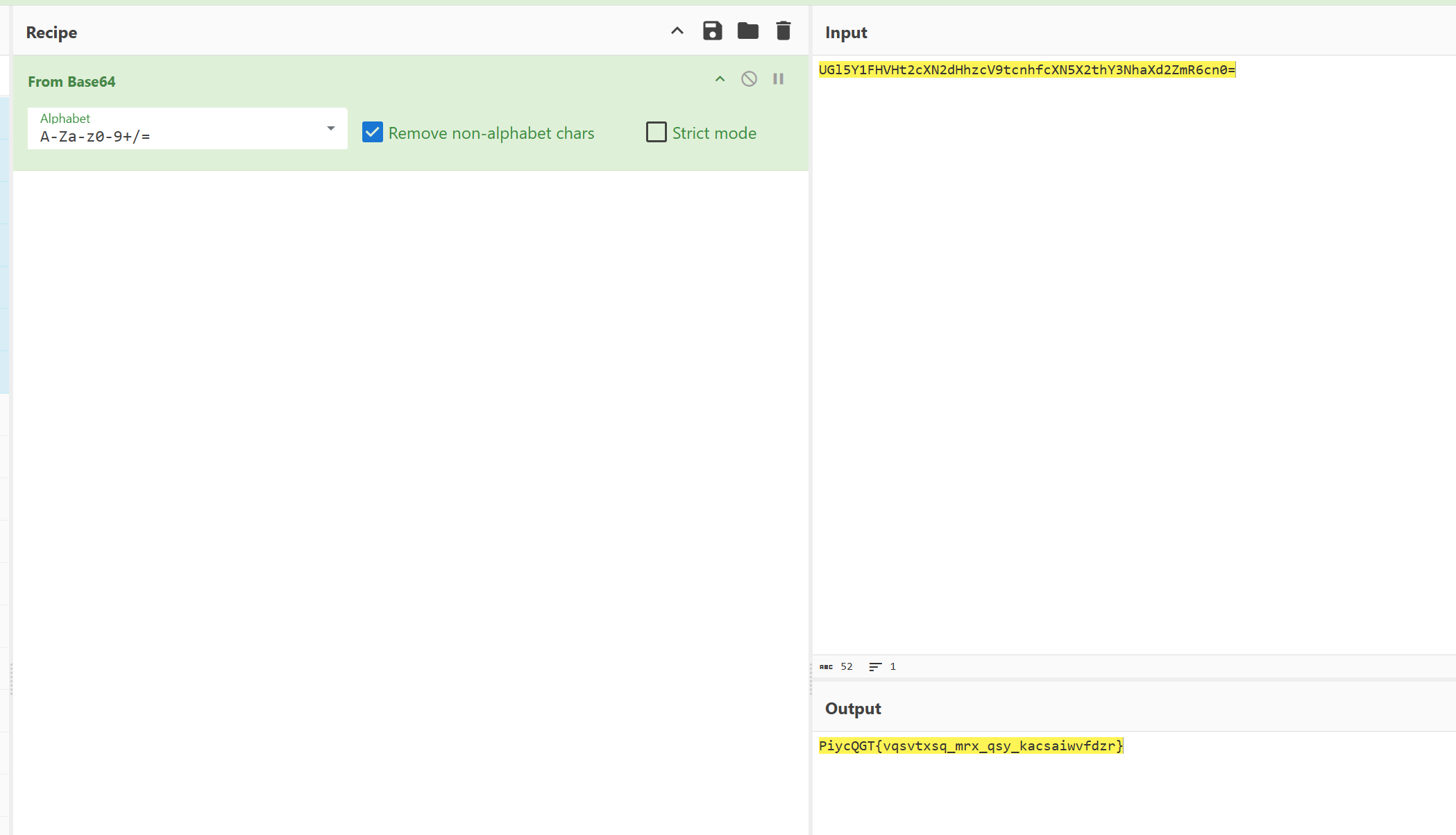
CyberChef Base64 decode – intermediate Vigenère ciphertext revealed
The { and } structure was preserved, confirming this is the flag format after one layer of decoding.
Step 2 - Vigenère Decode
Adding a Vigenère Decode step to the CyberChef recipe with key DEFCONONE produced the final flag:
- Recipe: From Base64 → Vigenère Decode (key:
DEFCONONE) - Input:
UGl5Y1FHVHt2cXN2dHhzcV9tcnhfXN5X2thY3NhaXd2ZmR6cn0= - Output:
MetaCTF{[redacted]}
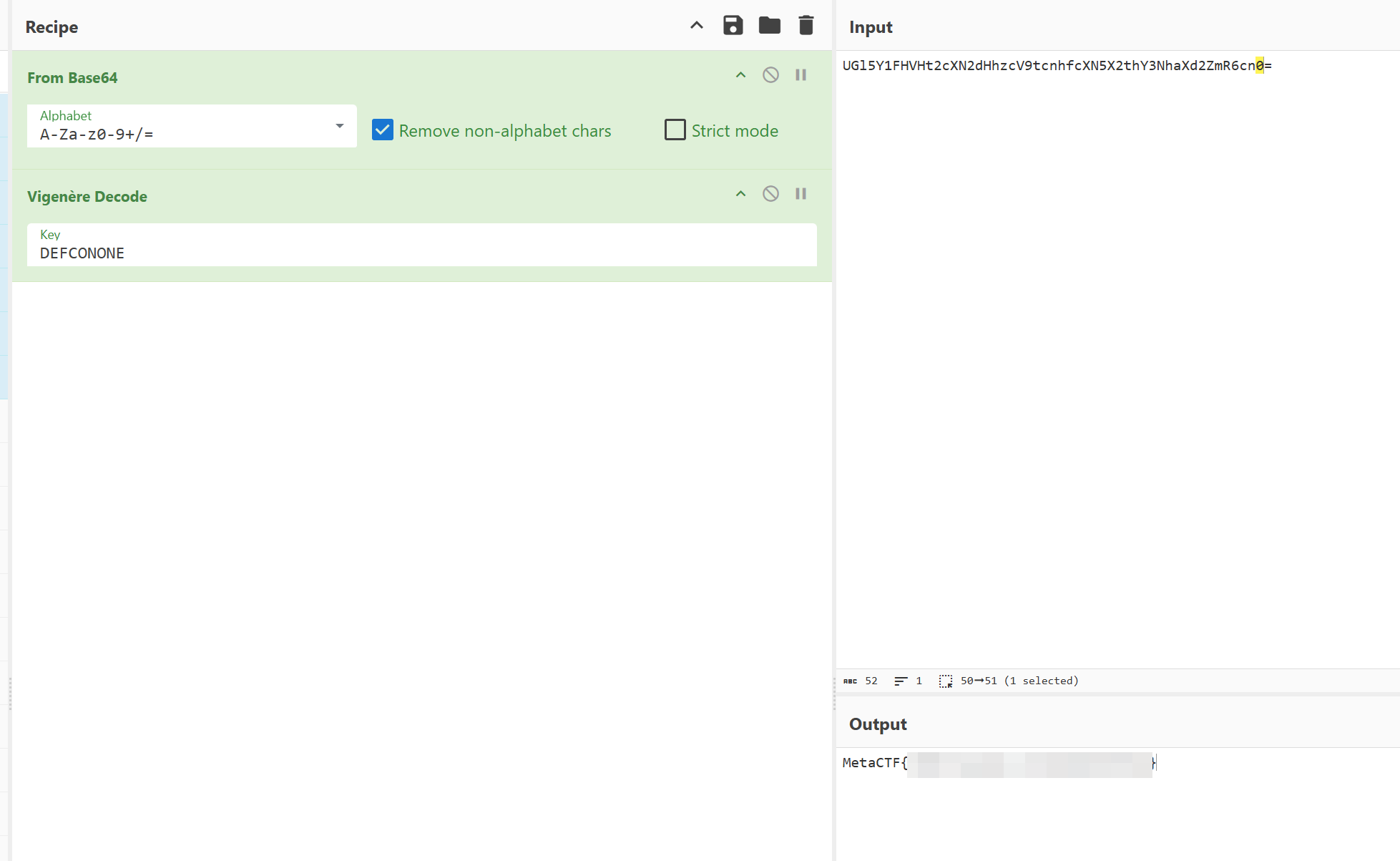
CyberChef Base64 + Vigenère decode – flag recovered using the DEFCONONE key
Result
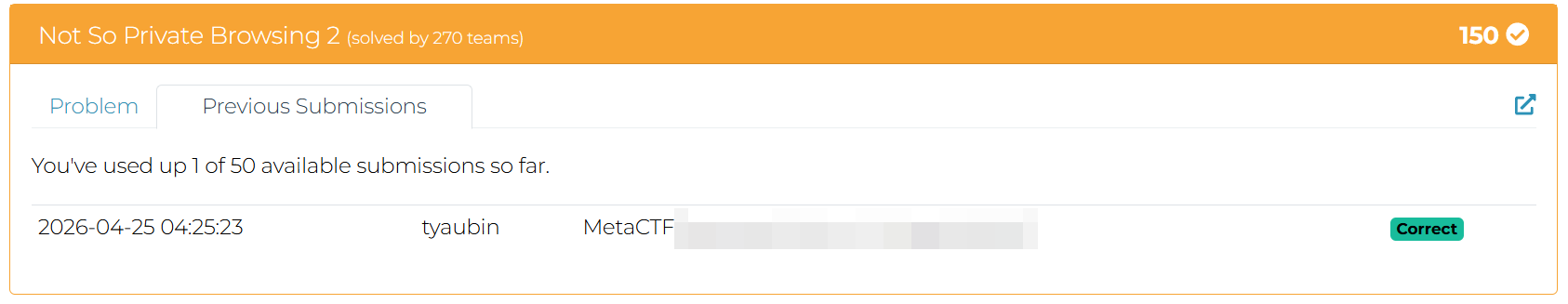
Flag submitted and marked correct
Takeaways
- Multi-layer encoding (Base64 wrapping a Vigenère cipher) adds steps but not real security when the encoding is detectable by structure.
- The
=padding on the ciphertext immediately identified Base64 without needing to try other encodings. - In-narrative hints (cipher specialists in France, key in the voicemail) guided the decoding approach - challenge flavour text is worth reading carefully.
- The Vigenère cipher is substantially stronger than ROT13 but still falls to known-plaintext attacks or a recovered key, as demonstrated here.